REFERENCES
- Abed, S., Jaffal, R., Mohd, B.J., Alshayeji, M. 2019. FPGA modeling and optimization of a SIMON lightweight block cipher. Sensors, 19, 913.
- Acholli, S., Ningappa, K.G. 2019. VLSI implementation of hybrid cryptography algorithm using LFSR key. International Journal of Intelligent Engineering and Systems, 12, 10–19.
- Bache, F., Schneider, T., Moradi, A., Giineysu, T. 2017. SPARX-A side-channel protected processor for ARX-based cryptography, Design, Automation & Test in Europe Conference & Exhibition (DATE), Lausanne, 990–995.
- Dehnavi, S.M., Rishakani, A.M., Shamsabad, M.M., Maimani, H., Pasha, E. 2016. Cryptographic properties of addition modulo 2n. IACR Cryptology ePrint Archive 181.
- Devi, D.I., Chithra, S., Sethumadhavan, M. 2019. Hardware random number generator using FPGA, Journal of Cyber Security and Mobility, 8, 409–418. doi: https://doi.org/10.13052/jcsm2245-1439.841
- Justin, R., Mathew, B.K., Abe, S. 2016. FPGA implementation of high quality random number generator using LUT based shift registers, International Conference on Emerging Trends in Engineering, Science and Technology ICETEST 2015, Science Direct Procedia Technology 24, 1155–1162.
- Katagi, M., Moriai, S. 2008. Lightweight cryptography for the internet of things; Sony corporation, 7–10. http://dx.doi.org/10.1016/j.istr.2012.10.005
- Khanam, R., Rahman, A., Pushpam, May, 2017. Review on reversible logic circuits and its application, 2017 International Conference on Computing, Communication and Automation (ICCCA2017), 5–6.
- Kumar, V.G.K., Rai, S.C. 2019. Implementation and analysis of cryptographic ciphers in FPGA. In: Abraham A., Dutta, P., Mandal, J., Bhattacharya, A., Dutta, S. (eds) Emerging Technologies in Data Mining and Information Security. Advances in Intelligent Systems and Computing, 755. Springer, Singapore. https://doi.org/10.1007/978-981-13-1951-8_59.
- Li, S., Song, H., Iqbal, M. 2019. Privacy and security for Resource-constrained IoT devices and networks: Research challenges and opportunities. Sensors, 19, 1935.
- McKay, K.A., Bassham, M., Turan, M.S., Mouha, N. 2016. DRAFT NISTIR 8114 report on lightweight cryptography, National Institute of Standards and Technology Internal Report 8114.
- Mohd, B.J., Hayajneh, T., Vasilakos, A.V. 2015. A survey on lightweight block ciphers for low-resource devices: Comparative study and open issues. Journal of Network Computer Applications. 58, 73–93.
- Patel, S.T. Mistry, N.H. 2015. A survey: lightweight cryptography in WSN, in International Conference on Communication Networks (ICCN). IEEE.
- Poojari, A., Nagesh, H.R., Kumar, K.V.G., Rai, S.C. 2020. A novel key scheduling algorithm for lightweight cryptographic applications, International Journal of Advanced Trends in Computer Science and Engineering, 9, https://doi.org/10.30534/ijatcse/2020/96912020
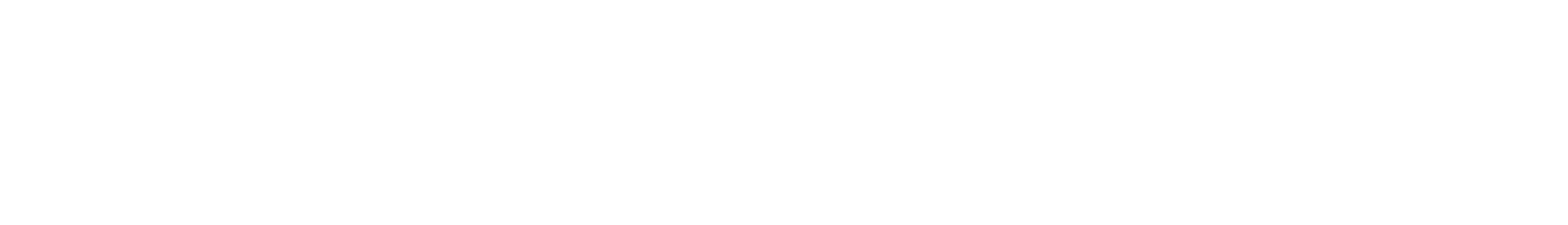
- Priyanka, M.P., Prasad, E.L., Reddy, A.R. 2016. FPGA implementation of image encryption and decryption using AES 128-bit core, 2016 International Conference on Communication and Electronics Systems (ICCES), Coimbatore, 1–5.
- Rana, S., Hossain, S., Shoun, H.I., Kashem, M.A. 2018. An effective lightweight cryptographic algorithm to secure resource-constrained devices, International Journal of Advanced Computer Science and Applications (IJACSA) 9. http://dx.doi.org/10.14569/IJACSA.2018.091137
- Sruthi, N., Nandakumar, R., Rajkumar, P. 2016. Design and characterization of HIGHT cryptocore, 2016 International Conference on Signal Processing, Communication, Power and Embedded System (SCOPES), Paralakhemundi, 205-209. https://doi.org/10.1109/SCOPES.2016.7955798.
- Teh, J.S., Teng, W., Samsudin, A., Chen, J. 2020. A post-processing method for true random number generators based on hyperchaos with applications in audio-based generators. Front. Comput. Sci. 14, 146405. https://doi.org/10.1007/s11704-019-9120-2.
- Usman, M., Ahmed, I., Aslam, M.I., Khan, S., Shah, U.A. 2017. SIT: A lightweight encryption algorithm for secure internet of things. International Journal of Advanced Computer Science and Applications(ijacsa), 8, http://dx.doi.org/10.14569/IJACSA.2017.080151.
- Vergos, H.T., Efstathiou, C., Nikolos, D. 2002. Diminished-one modulo 2n + 1 adder design, IEEE Transactions on Computers, 51, 1389–1399.
- Vishwakarma, P.P., Tripathy, A.K., Vemuru, S. 2020. Designing a cryptosystem for data at rest encryption in mobile payments. International Journal of Applied Science and Engineering, 17, 373–382. https://doi.org/10.6703/IJASE.202012_17(4).373
- Wang, Z., Jullien, G.A., Miller, W.C. An algorithm for multiplication modulo (2^N-1), ASILOMAR '95 Proceedings of the 29th Asilomar Conference on Signals, Systems and Computers (2-Volume Set), 956.
- Weber, M., Boban, M. 2016. Security challenges of the internet of things, 2016 39th International Convention on Information and Communication Technology, Electronics and Microelectronics (MIPRO), Opatija, Croatia, 638–643, doi: 10.1109/MIPRO.2016.7522219.
- Zhang, X. 2011. Reversible data hiding in encrypted image, in IEEE Signal Processing Letters, 18, 255–258, doi: 10.1109/LSP.2011.2114651.
- Zhang, X. 2012. Separable reversible data hiding in encrypted image, in IEEE Transactions on Information Forensics and Security, 7, 826–832, doi: 10.1109/ TIFS.2011.2176120.
- Zimmermann, R. Apr. 1999. Efficient VLSI implementation of modulo 2 n ±1 addition and multiplication, Proc. 14th IEEE Symposium on Computer Arithmetic, 158–167.