Hung-Yu Chien* and Ru-Yu Lin Department of Information Management, Chaoyang University of Technology, Wufong, Taichung County 41349, Taiwan, R.O.C.
Download Citation:
|
Download PDF
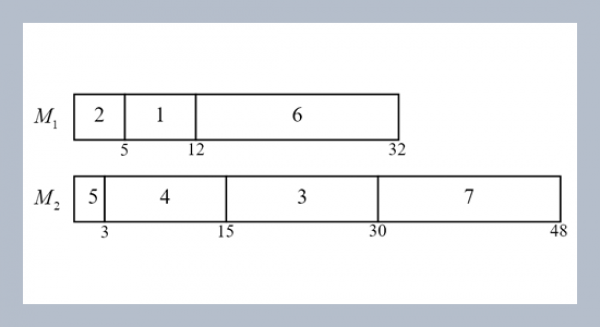
This paper examines the security weaknesses of Lin, Huang and Lin’s tripartite authenticated key agreement scheme, and proposes our new scheme. The proposed scheme resists all the security threats and further provides key confirmation. The scheme is very simple and efficient.ABSTRACT
Keywords:
Weil pairing; elliptic curve; authenticated key agreement.
Share this article with your colleagues
[1] Lin, C. H., K. J. Huang, and S. S. Lin. 2004. Improving Shim’s tripartite authenticated key agreement protocol based on Weil pairing. ISC: 250-255.REFERENCES
[2] Boneh, D. and M. Franklin. 2001. Identity-based encryption from the Weil Pairing. Advances in Cryptology Crypto’01, Santa Barbara, CA, USA, August: 213-229.
[3] Silverman, J. H. 1986. “The arithmetic of elliptic curves”. GTM 106, Springer-Verlag.
[4] Shim, K. 2003. Efficient one-round tripartite authenticated key agreement protocol from Weil pairing. Electronics Letters, 39, 2: 208-209.
[5] Chen, L. and C. Kudla. 2002. “Identity Based Authenticated Key Agreement Protocols from Pairings”. IACR, Report.
[6] Joux, A. 2000. A one round protocol for tripartite Diffie-Hellman. ANTS IV, LNCS1838, Spring-Verlag: 385-394.
[7] Boneh, D. B. Lynn, and H. Shacham. 2001. Short signatures from the Weil pairing. In C. Boyd, editor, Advances in Cryptology-Asiacrypt 2001, LNCS 2248, Springer-Verlag: 514-532.
[8] Al-Riyami, S. S. and K. G. Paterson. 2002. “Tripartite authenticate key agreement protocols from Paiiring”. Cryptology ePrint Archive, Report.
ARTICLE INFORMATION
Accepted:
2005-03-08
Available Online:
2005-04-03
Chien, H.-Y., Lin, R.-Y. 2005. An improved tripartite authenticated key agreement protocol based on weil pairing, International Journal of Applied Science and Engineering, 3, 13–18. https://doi.org/10.6703/IJASE.2005.3(1).13
Cite this article: